VLAN tagging on OpenWRT/managed switches
(Updated: )
I wanted to place my router somewhere not in the meterkast, so I used VLAN tagging on a managed switch to get the WAN data to the router and my LAN data back on the same wire (but different VLAN) to distribute to the rest of the house.
VLAN in theory ¶
VLANs (Virtual LAN) are a way of segregating traffic virtually without the need for separate cables. This can be very useful in business setup to separate different access/security zones (e.g. finance vs development departments). (Dutch) ISPs also use it to separate TV from Internet traffic. For example, Telfort uses VLAN 34 (telfort.nl) and XS4ALL uses VLAN 6 (xs4all.nl).
VLAN in practice ¶
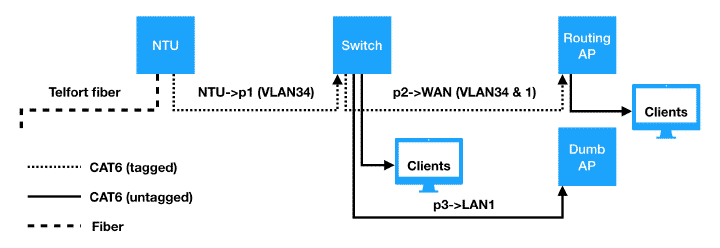
I use VLANs to forward all WAN traffic via a managed switch to my router which then NATs the connection and takes care of DHCP/DNS etc. I then return the LAN traffic from the router back to the switch over the same cable, but different VLAN, such that the switch can then distribute the LAN connection to further devices.
Hardware used:
- Telfort NTU (telfort.nl)
- Netgear GS108E v3 managed switch (tweakers.net)
- Archer C7 v2 (tweakers.net) with OpenWRT
Configuration on router and switch ¶
On my switch, I receive WAN traffic (VLAN34) on port1, and use port2 to both forward the WAN traffic to my NAT’ing router, as well as receiving the LAN traffic back from the router:
VLAN config: which ports are part of which VLAN: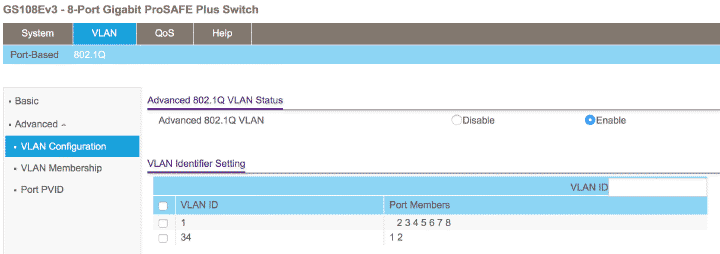
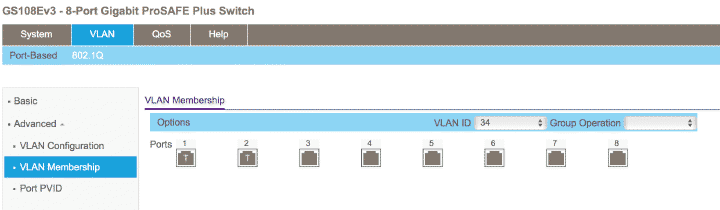
VLAN membership: for each VLAN, should ports tag outgoing packets or not (redundant info with above)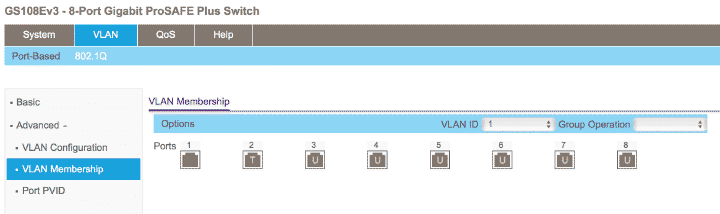
Port PVID: for incoming untagged packets, which VLAN should these be treated as?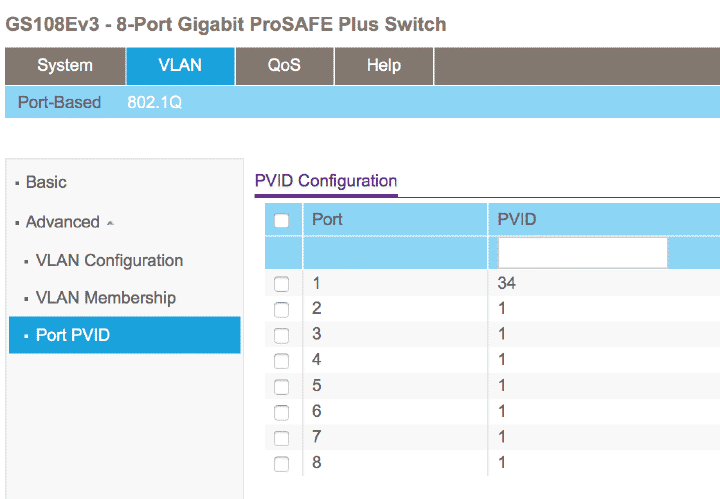
On the NAT’ing router, I configure the WAN port to handle both VLAN34 and VLAN1 traffic. Since this is going over one wire, the packets need to be tagged (else they could not be distinguished). The other ports are also part of VLAN1, but are untagged, such that clients do not notice anything of the VLAN, see below: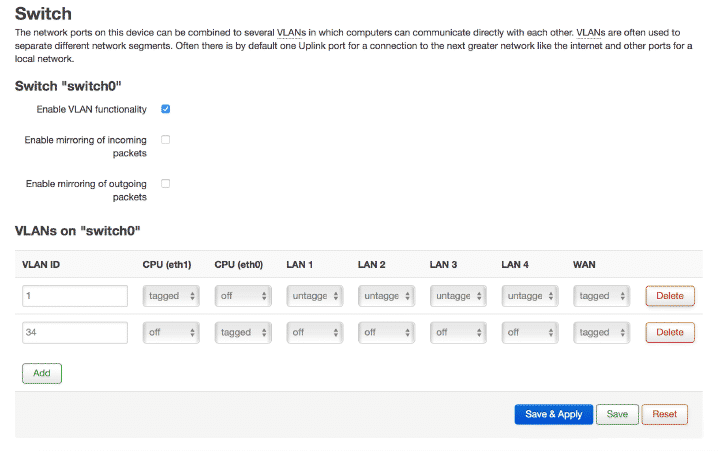
Once configured, the WAN traffic will arrive at the switch, be forwarded to the router, then go through NAT, after which they will go to the client, which could mean the packet travels back to the switch.